by Josh Ryan | Mar 8, 2023 | Security
As anyone with a mobile phone in Australia knows, scams are on the rise. Whether it’s “mum” asking you send through a couple hundred bucks on loan for groceries, or “Linkt” asking you to top up your toll account, sometimes fraudulent and scammy characters can be hard...

by Josh Ryan | Jan 31, 2023 | Security
Late last year, Google announced that Chrome will no longer be supported on Windows 7 or Windows 8/8.1. Their newest version of Chrome (Chrome 110) is set to be released on February 7th. This newest version will be the first to require you running Windows 10 or...

by Josh Ryan | Dec 15, 2022 | Microsoft 365, Security
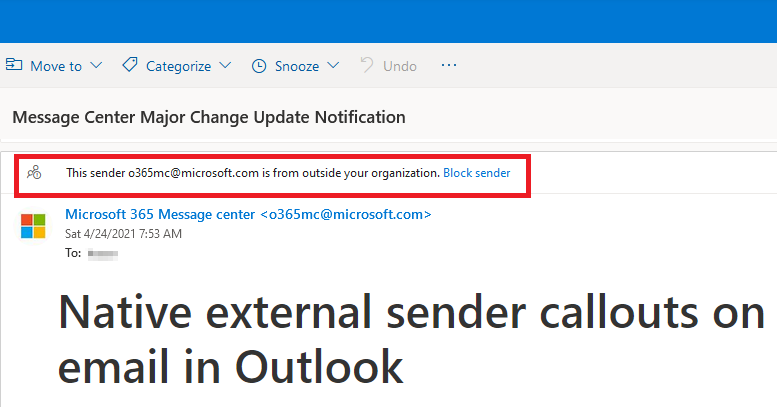
We’ve recently had several clients come to us asking to remove the external email warning tag on their business’ Microsoft Outlook. Our guidance, however, is that tag should be kept as its benefits far outweigh the cons. Let’s run through why. What is the external...

by Josh Ryan | Aug 16, 2022 | Microsoft 365, Security
If you need help setting up Multifactor Authentication (MFA) for your Office 365 Account – This guide will walk you through the process. Please note: Multifactor will need to be enabled on your account before proceeding. Let us know before continuing so we can set...

by Josh Ryan | Aug 25, 2021 | Security
Whether we like it or not, passwords are the key to almost everything we do online – from dating apps, accessing your bank to logging into your M365 account. These days especially, with accounts and sign-in required for almost everything, strong password management...

by Josh Ryan | Jul 28, 2021 | Security
The outbreak of COVID-19 may have shifted the way we work forever. Or, at the very least, it sped-up existing trends. Businesses have had to adapt to support their employees working remotely. As a result, team chat applications are, in many ways, becoming the modern...